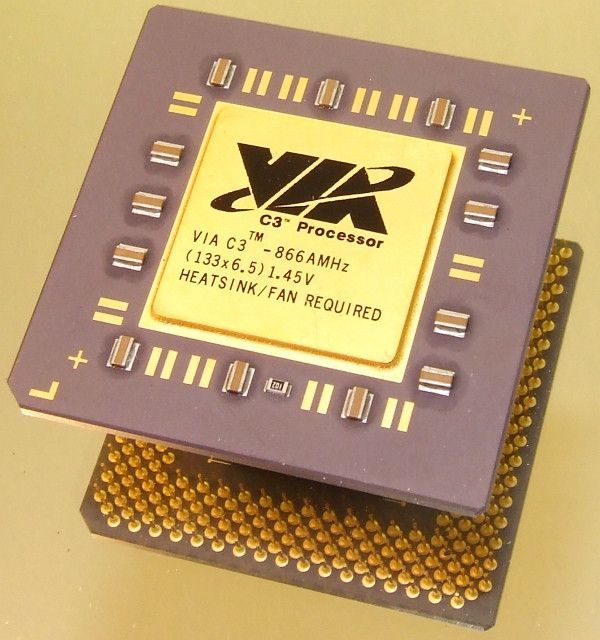
VIA C3 processors are probably only a tiny part of the desktop PC market share, and their manufacturers only market the chip in pre-assembled devices such as digital signage booths, information stands, ticket machines, ATMs, etc.. (which do not require much computing power).
Accessing root privileges under Linux on a machine with a VIA C3 CPU is very easy.
At the Black Hat 2018 conference, security researcher Christopher Domas discovered that accessing root privileges under Linux on a VIA C3 processor-based machine “Nehemiah” is ridiculously simple: “Just type”.byte 0x0f, 0x3f” (without quotes) into any Linux CLI in user mode, and voila! You are now the primary user of this system.”
This backdoor, probably placed by the designers of the processor, completely collapses the operating system’s ring-shaped permission system and lifts users and applications from the 2-ring (and higher) user area to the 0-ring (root). It is an exploitation of a shadow core, a RISC processor hidden in C7, which manages the start, operation and key storage of x86 cores. Intel and AMD also have’shadow cores’ with similar functions.
It would be so easy to be root users under Linux under a VIA C3 processor and show how vulnerable it could be to manipulate the computers equipped with this type of chips, the challenge would be to first access the machines and computers that run them, that’s another story.